Last update images today As Other States Rally To Aid Texas Untitled Design 8 Heat Map Cyber Security















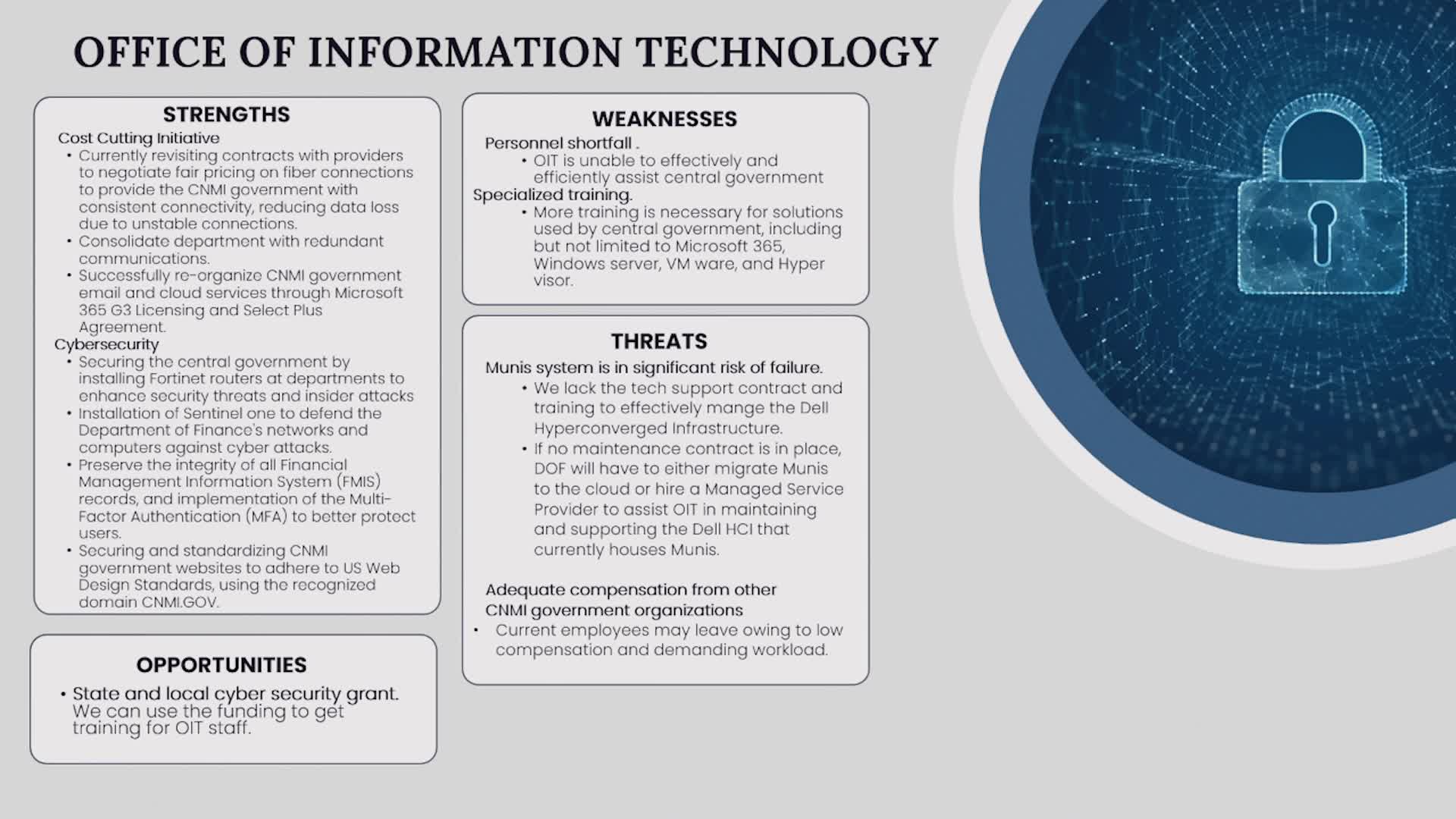
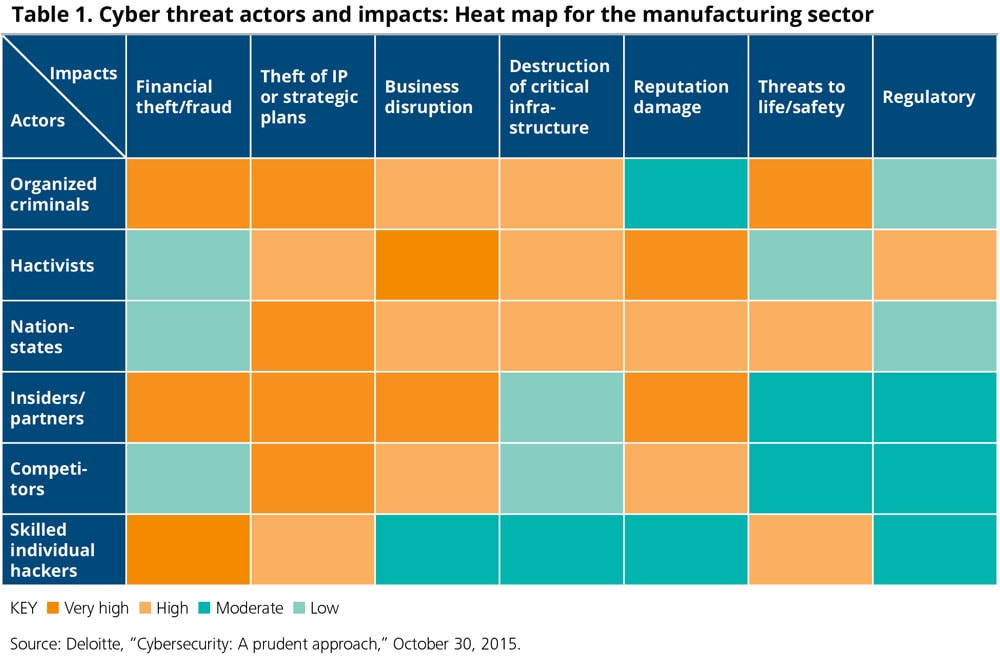
Cyber security sectoral analysis - 3.3 960 X 640 Cyber Heat Map Actionable Cybersecurity - 68588f63e2b68c22adf0fe89 847e3ff38071e26c8cb363c7e62f5880 Cyber%20Heat%20Map%20 %20Holistic%20Actionable%20Cybersecurity%20Roadmap P 500 7 free cyber threat maps showing - Cyber Threat Maps 650 Risk Heat Map A Powerful Visualization - Risk Hear Map Powerful Tool E1553538402490 1 As other states rally to aid Texas - Untitled Design 8 4 Steps to a Smarter Risk Heat - Heat Map 1 Titomic Making a splash in the - MediaChromedll First see pic carefully - Media
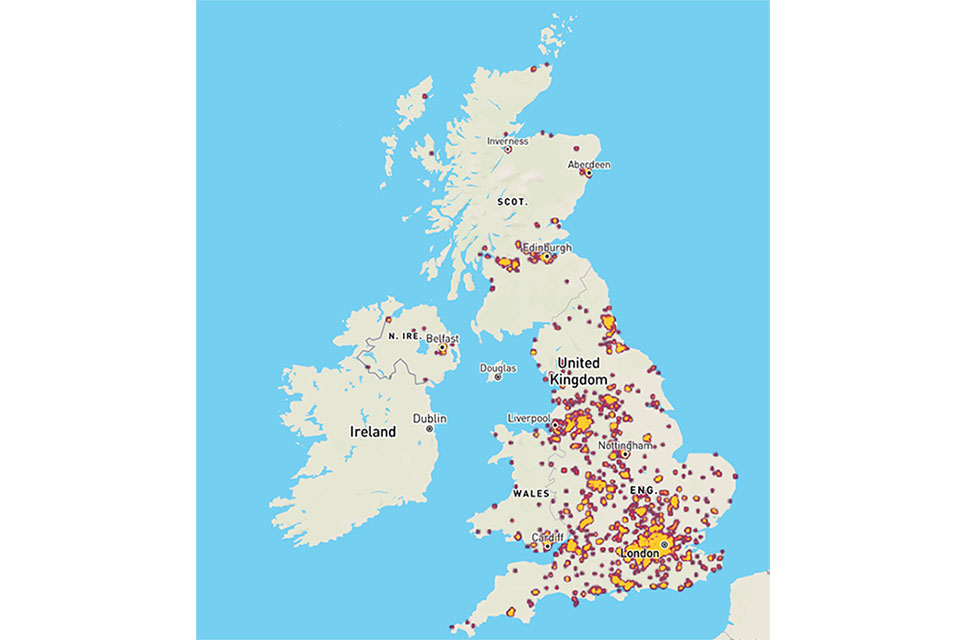
Information On Some Security Products - RiskHeatMap Figure 1 Risk Matrix The Protiviti - Figure 1 Risk Matrix Cyber security sectoral analysis - Wales 960 X 640 Cherry Point wins 2024 DOE award - 1fa191b4 B391 4ea2 Dea3 D6ec5938c746 40efc1dba5114ffeb45230c89ac93c9dWeatheralertdaygraphic Cyber Attack Map - Fortinet Threat Map Cyber Security Padlock and Chain - Cyber Security Padlock Chain Against Pulsating Circles Over World Map Blue Background Computer Technology Concept 310886029 How to create a cyber security - Heat Map.width 660.format Jpeg Quality 90 Heat Map Template for PowerPoint - Heat Map Template For PowerPoint Jpg Webp.webp
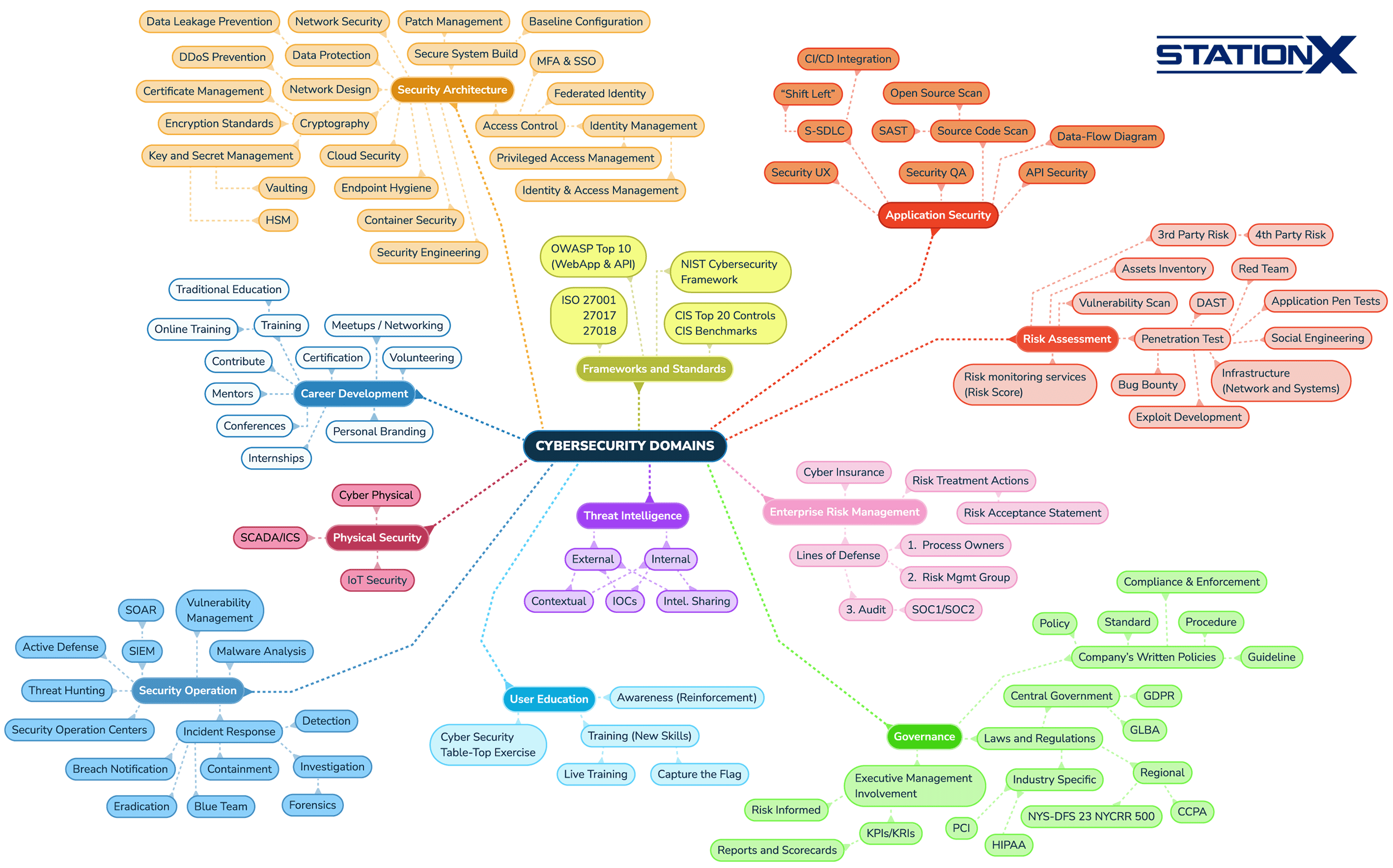
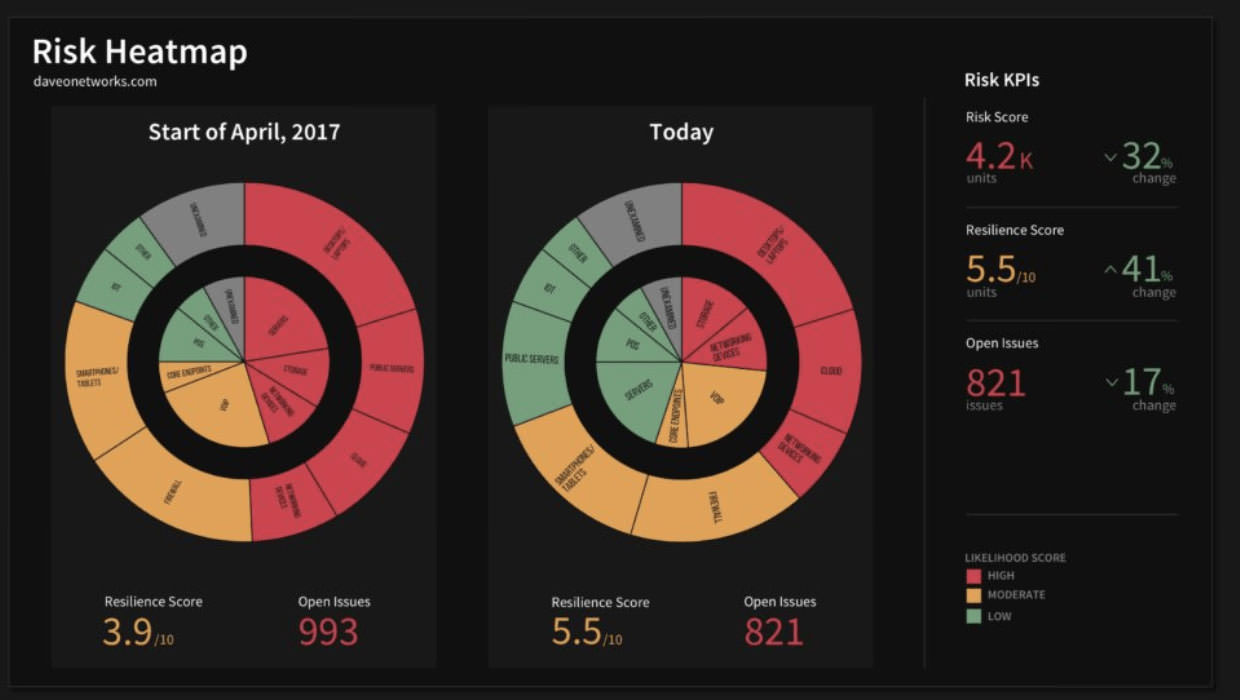
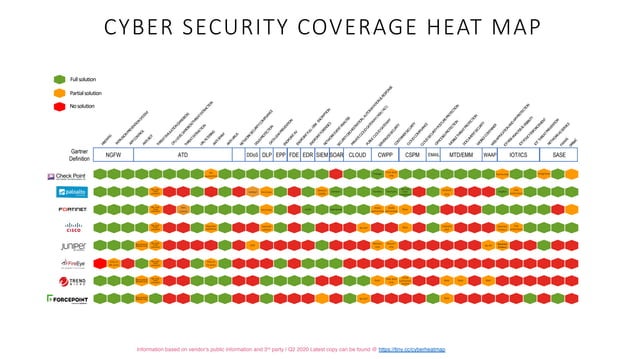
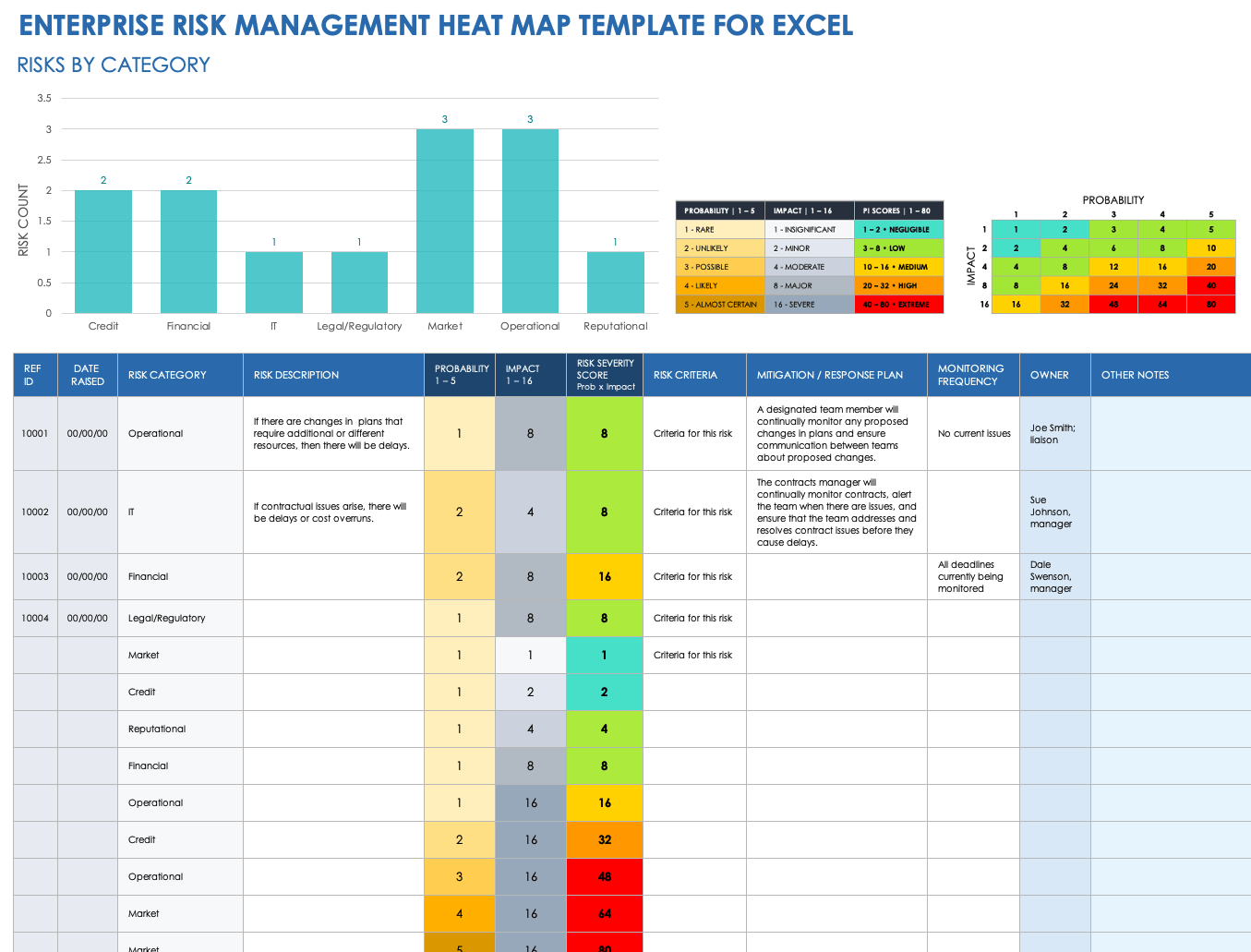
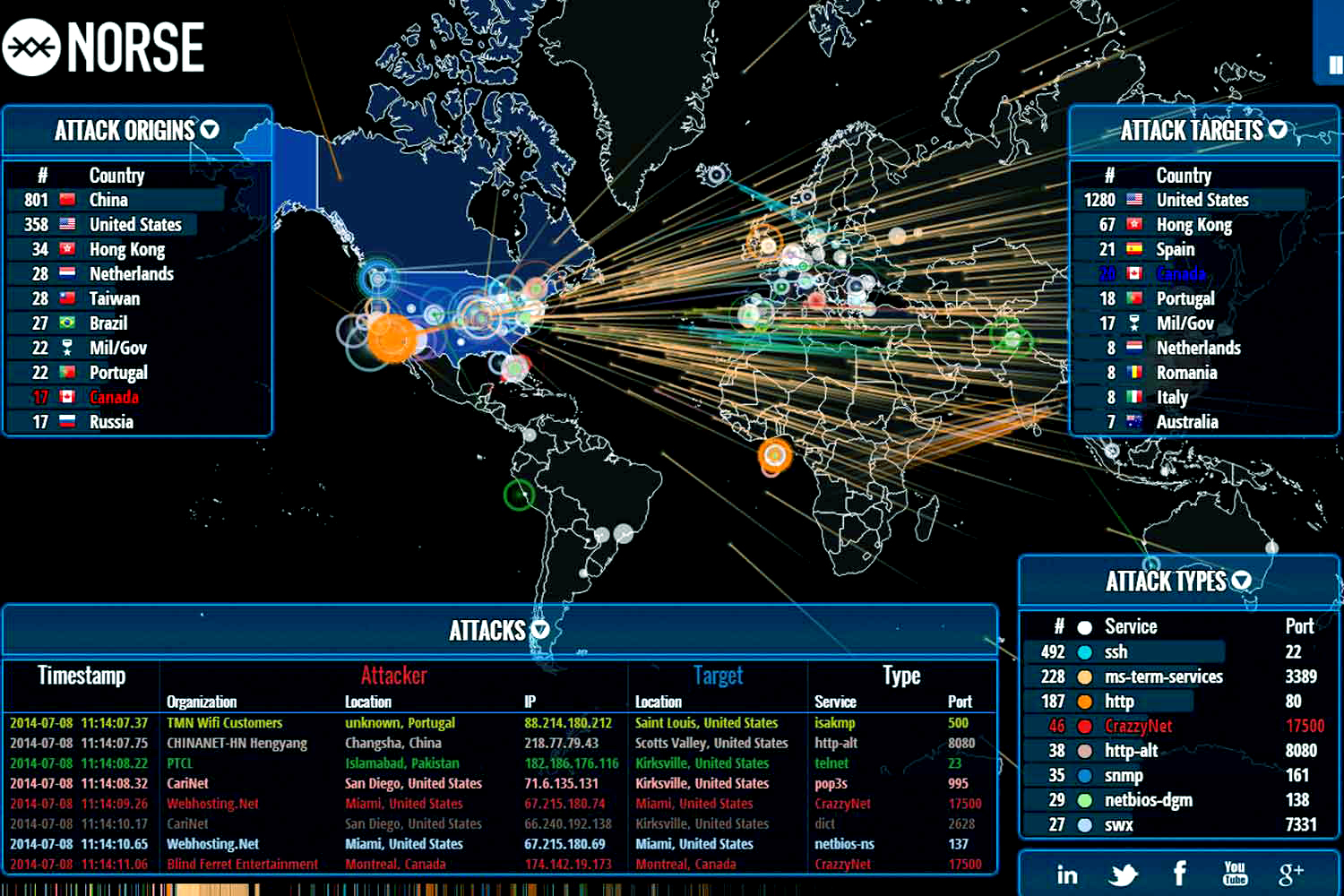
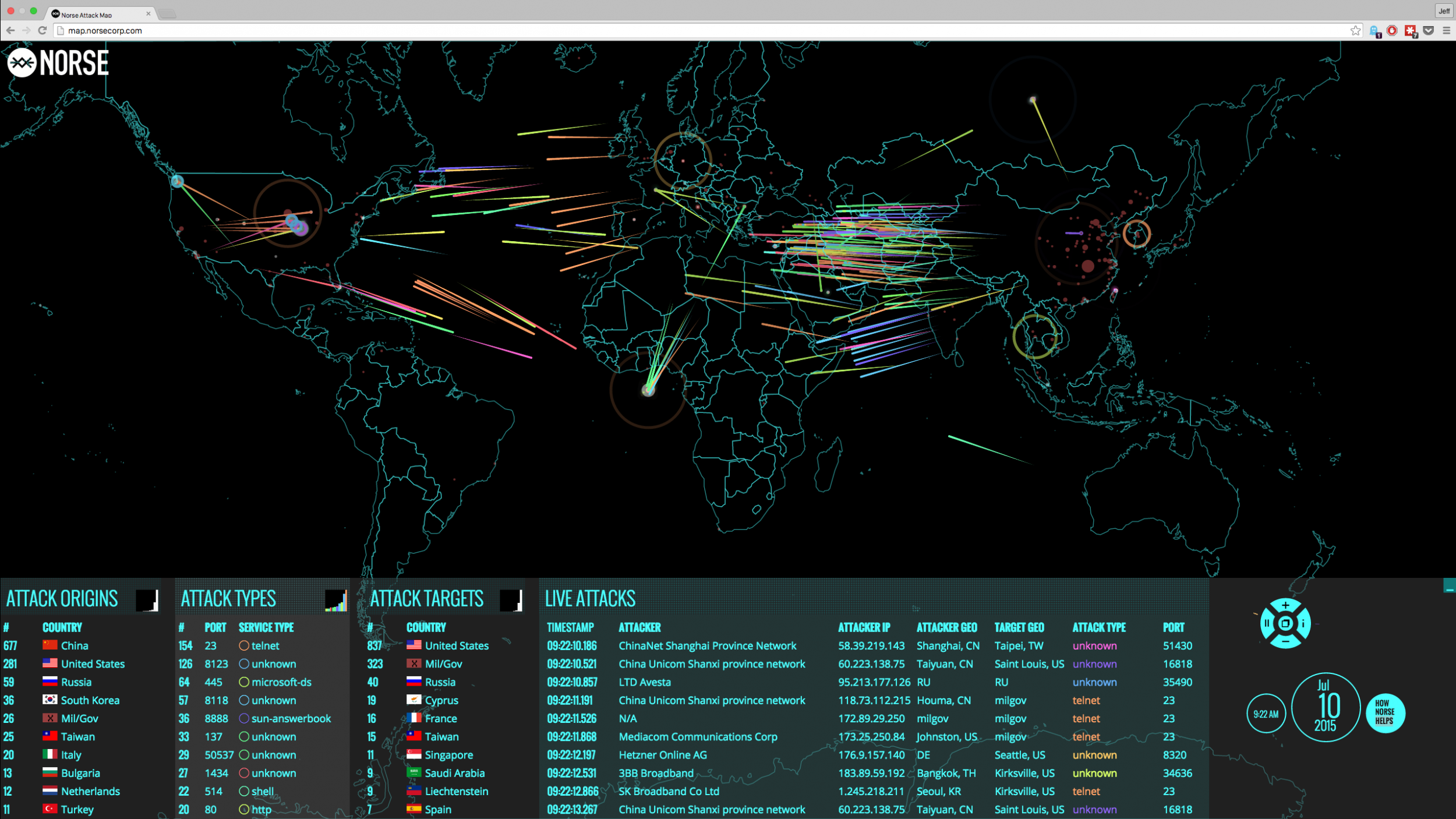
Cyber Security Coverage heat map - Cyber Security Coverage Heat Map 1 638 As other states rally to aid Texas - Untitled Design 9 Real Time Cyber Threat Maps YouTube - Maxresdefault National Cyber Group Tech Details - E9lyywdbfec5atg156klReal Time Cyber Attack Map Shows - Norse Live Attack Map 3 Cyber Security Domains - StationX Cyber Security Domains V1.1 2 Heat Map Analysis In Excel Design - IC Enterprise Risk Management Heat Map Template Heat Maps Latest News - Risk Heat Map
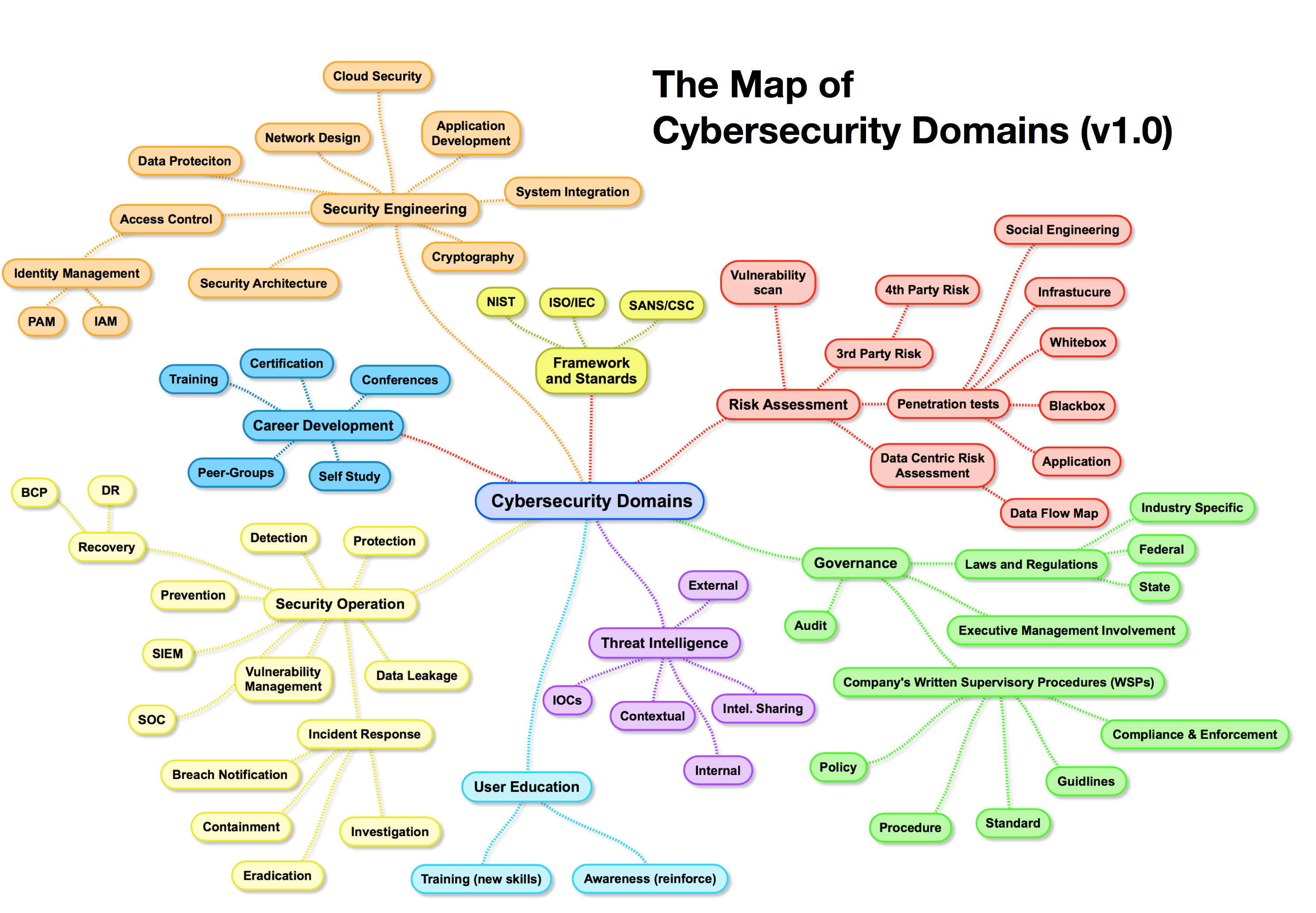
Top 10 Cyber Attack Maps to See - Top Cyber Attack Maps Top 15 Live Cyber Attack Maps for - Kaspersky Map Cybersecurity Supply And Demand - Dd9cc55a2fe4d8b16841187f793f74db Main areas of security - Cybersecurity Map 1.0 Beat the heat with these cooling - 6871e0a7e6ec0 Media 7a01d82a955d4e96b447b72666824fe5 DMID1 67lxba0fg 640x480 Pulsar Security News amp Analysis - Kod0hstbiolbzunvtjxyReconmap News Analysis - Wxquljcjpjozvjvo42awCybersecurity Risk Assessment Program - Cybersecurity Risk Assessment Program Mapping Of Multiple Cyber Attacks Using Risk Heat Map Slide01
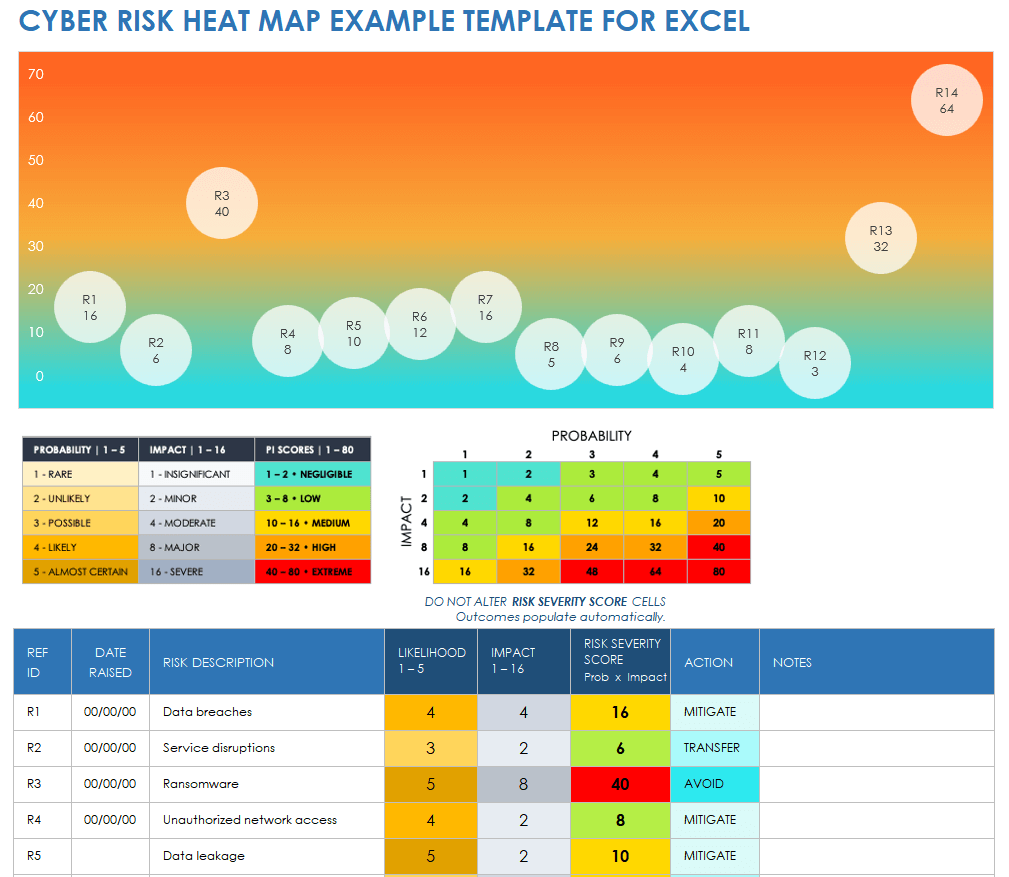
Top 15 Live Cyber Attack Maps for - Fireeye Map Pre Adoption Security Readiness - Security Readiness Scenario Img Cyber Threats amp Security Facts - Unika Infocom Cyber Threat Map 1 Cyber threat heat map feryinside - Cyber Attack Maps Are A Trove Of Information 468629 3 Cyber CI Technologies Tech Details - Ackorbmqaqwxt5q0i5rr Cybersecurity through information - Career%20Map%20for%20Infromation%20Security Free Risk Heat Map Templates - IC Cyber Risk Heat Map Example Template What is a Heat Map in Cyber Security - Canva MADmwAd Jfw
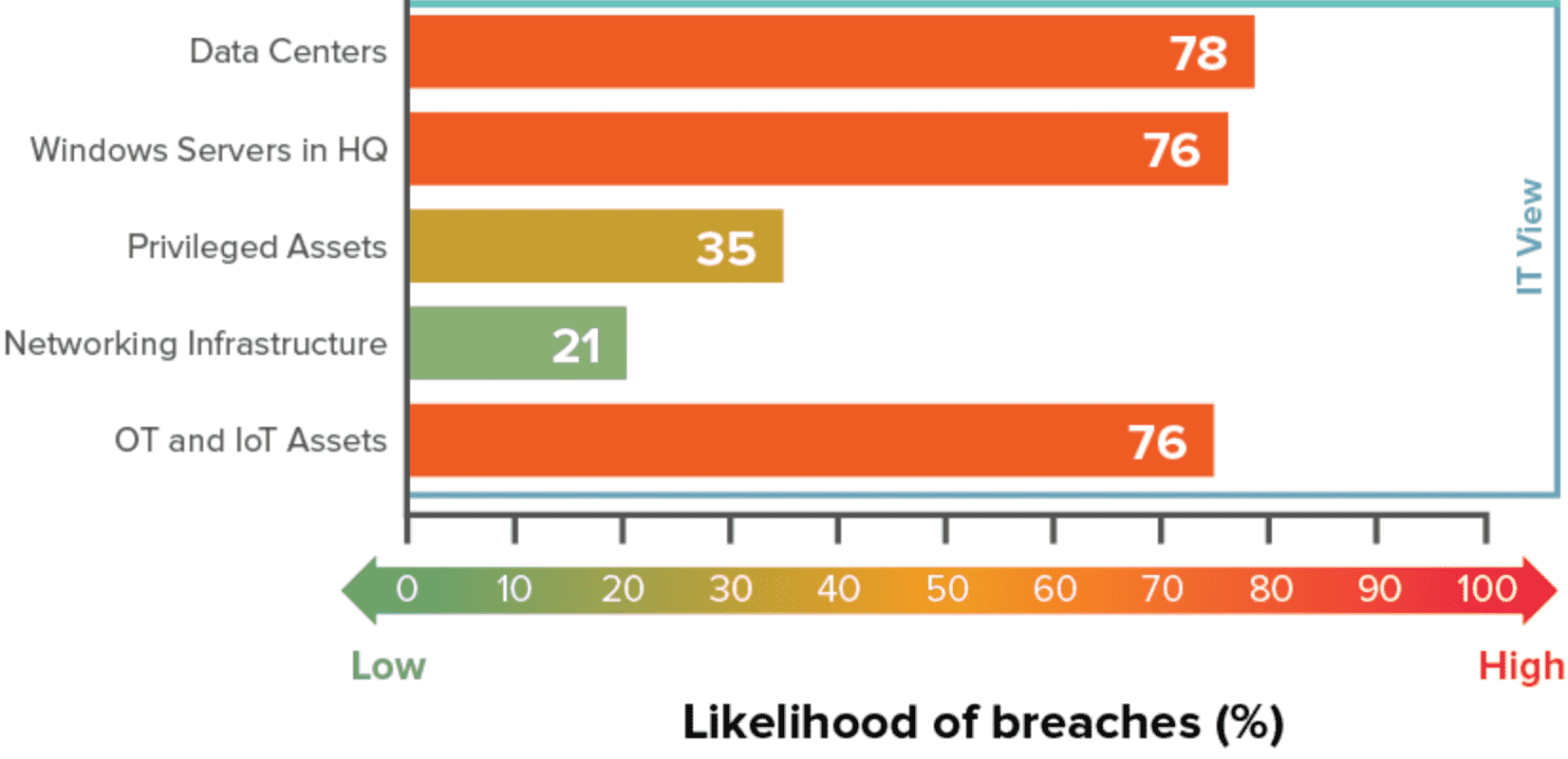
The Ultimate Guide To Cyber Threat - Cyberattackmap 1024x683 US National Cybersecurity Strategy - JfNWSd8pB3k6aSjJHpXW3B3GBTu2C3JkPJEdf4WXVeU.JPGCitizenPortal ai City IT Department - Thumbnail 4224175 Reconmap Profiles Contacts - Ybwr5vujx9gt23a7a2oy Groslive Blog - Heat Map It View Why Understanding RISK is Central - Risk%20Heat%20Map%201 Top 10 Risk Heat Map Templates - Enterprise Risk Assessment Heat Map Why Cyber Risk Needs Numbers - 1744371965738
Cherry Point wins 2024 DOE award - 14dbdd24 Bad6 462d 9889 5c183b72750e MCASCherryPoint Cybervore Inc Tech Details - Dtti2pqozsoszqetqukxWhat is Lumma Stealer The malware - AA1Fdz5u.imgWebinar Stay Ahead of Cyber Economic - Cyber Economic Risk Education Business Conversations 1024x535 Cybersecurity capability and Risk - Heat Map What is a Risk Heat Map Benefits - Risk Heat Map Trimmed Why Your Business Needs a Security - Cyber Security Heat Map NATIONAL NEWS National Security - NEW HEADLINES NATIONAL2
NIST CYBERSECURITY FRAMEWORK iMindMap - 4GZYZCPf NIST CYBERSECURITY FRAMEWORK Mind Map Top 8 Cyber Threat Maps To Track - Best Threat Maps Cyber Security 2025 Test Bank - Maxresdefault Additive manufacturing and cyber - 3D Opportunity Risk Management Table1

